CASE STUDY SNAPSHOT
Customer : An leading Industrial Equipments OEM.Size : >1000 – 10000
Project vertical : Industrial
Challenge : Develop a secure firmware update solution for iMx6 based Edge Devices.
Solution : Design and develop an Asymmetric Encryption based Secure Update mechanism Flexible FOTA Strategy
Services & Products Availed : Product engineering services, Secure Firmware Updates, Embedded System Security
Tools and Technologies :
- Key Hardware: NXP i.Mx 6, HSM
- Software Development: JC, C++
- Frameworks: AES 256, ECDSA, ECDH
- Peripherals: PKI, Yocto based Linux
INTRODUCTION
A Fortune 100 Industrial OEM, specializing in robust IoT gateways for edge devices, faced escalating cyber threats in their i.MX6-based systems. With the surge in IoT deployments like machine health monitors and vehicle trackers, they needed a secure firmware update (FOTA) solution to deliver OTA updates, bug fixes, and vulnerability patches without risking unauthorized access or tampering, ensuring compliance and operational continuity.
CHALLENGE
The industrial OEM grappled with unique hurdles in securing firmware updates for their edge devices amid a booming IoT landscape. Rapid deployment of connected systems such as smart industrial sensors and remote monitoring gateways amplified cyber vulnerabilities, including man-in-the-middle attacks, firmware tampering, and data breaches during OTA transmissions. Traditional update methods exposed devices to risks like reverse engineering of packages or exploitation of unpatched flaws, potentially halting production lines or leaking sensitive operational data. Offline updates via USB or memory cards were equally perilous, lacking encryption and validation, while regulatory demands for cyber-secure IoT solutions intensified pressure. Balancing seamless feature additions and bug fixes with ironclad protection against evolving threats like ransomware targeting industrial controls demanded an end-to-end FOTA framework resilient to both online and offline scenarios, all while minimizing downtime in mission-critical environments.
SOLUTION
Embien, a premier IoT design and engineering firm specializing in secure firmware updates and cyber-secure edge devices, rose to the occasion by delivering a comprehensive Secure FOTA solution tailored for the Fortune 100 Industrial OEM's i.MX6-based IoT gateways. Our approach began with a thorough threat assessment, profiling potential attack vectors such as unauthorized code injection, eavesdropping on OTA channels, and rollback exploits in field-deployed devices. Leveraging our deep expertise in NXP i.MX processors, we integrated High Assurance Boot (HAB) mechanisms to establish an unbreakable chain of trust from power-on, ensuring only authenticated firmware could execute.
System Architecture
The cornerstone of our solution was the development of a dual architecture storage system using A/B partitioning to enable atomic updates and seamless rollbacks. We restructured the device's flash storage into three key partitions: the immutable Boot Loader for initial integrity checks, File System A as the primary active environment, and File System B as the secondary for staging updates. This design allowed the gateway to boot from the verified partition while preparing the alternate one, drastically reducing downtime during FOTA processes. For instance, upon initiating an OTA update, the new firmware package is downloaded to the inactive partition, validated, and only swapped upon success, safeguarding against bricked devices in harsh industrial settings.
Asymmetric Encryption based Security
Security was woven into every layer. We provisioned cryptographic keys via One-Time Programmable (OTP) fuses during manufacturing, rendering them tamper-proof against physical attacks. Asymmetric cryptography, including ECDSA for digital signatures, was employed to sign firmware packages, verifying authenticity and preventing man-in-the-middle interceptions. Packages bundled not just the binary but metadata like version manifests, license validations, and checksums, all encrypted with AES-256 for confidentiality during transit.
Flexible FOTA Strategy
To address both online and offline FOTA needs, we architected a hybrid delivery system. For OTA scenarios, updates are pushed via a dedicated Secure FOTA server hosted on a fortified cloud infrastructure, secured with TLS 1.3 for end to end encryption. Our team assisted the OEM in configuring AWS or Azure instances with automated workflows, including CI/CD pipelines scripted in Python for package generation and deployment. These scripts handle signing with Hardware Security Modules (HSMs), revocation list checks via OCSP, and anomaly detection to flag suspicious update requests. Offline mechanisms were equally robust: users could load encrypted packages via USB, with the device performing on the fly decryption using a dedicated secure element, the Microchip ATECC608. This crypto authenticated chip stores private keys in a protected enclave, immune to software based extractions, and supports ECDH for key exchange.
Threat modelling
End-to-end security extended to Public Key Infrastructure (PKI) setup, where Embien guided the OEM in establishing a root Certificate Authority (CA) for scalable certificate management. We implemented certificate pinning to mitigate rogue CA risks and automated CRL (Certificate Revocation List) distribution to instantly neutralize compromised keys. Threat modeling using STRIDE methodology uncovered edge cases like side-channel attacks on i.MX6's ARM Cortex-A9 core, prompting mitigations such as constant-time cryptographic operations to evade timing leaks.
System Hardening
Implementation involved iterative prototyping on Yocto based embedded Linux distributions, customized for the i.MX6's resource constraints. We optimized the FOTA agent, a lightweight daemon monitoring for updates via MQTT over TLS, to consume minimal CPU and memory, ideal for battery constrained edge devices. Rollback logic was battle tested in simulated failure modes, ensuring atomicity: if a post update boot fails integrity checks, the system reverts to the prior partition within seconds, logging diagnostics to a secure syslog for forensic analysis.
Beyond core FOTA, Embien enhanced the ecosystem with value-added tools. We also conducted penetration testing using tools like Metasploit and Burp Suite, achieving zero critical vulnerabilities and earning third-party cybersecurity certifications like IEC 62443 compliance for industrial IoT.
Our agile development cycle, spanning requirements gathering, PoC in two weeks, alpha beta testing, and production rollout in three months, ensured the solution scaled across the OEM's product lines, from rugged gateways to distributed sensor networks. By fusing secure boot, encrypted OTA/Offline FOTA, PKI orchestration, and rollback resilience, Embien transformed the OEM's edge devices into fortresses against cyber threats, empowering secure firmware updates that evolve with IoT demands. This holistic approach not only met but exceeded expectations, positioning the OEM as a leader in cyber secure industrial IoT.
BENEFITS
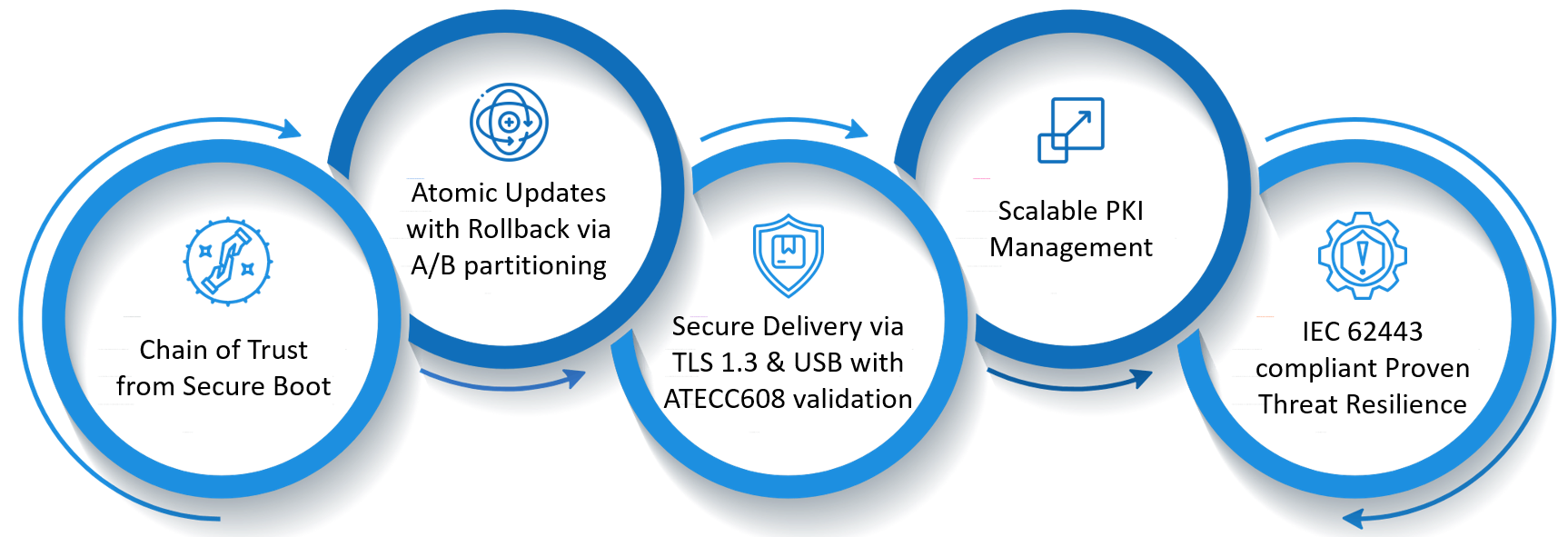
- Unwavering Chain of Trust: Implemented secure boot with HAB and OTP fuses on i.MX6, preventing unauthorized firmware execution and ensuring 100% boot integrity for edge devices.
- Atomic Updates with Rollback: A/B partitioning enables zero-downtime FOTA and instant recovery from failures, minimizing industrial disruptions and operational risks.
- Hybrid Secure Delivery: Supports encrypted OTA via TLS 1.3 and offline USB updates with ATECC608 secure elements, offering flexibility without compromising cyber security.
- Scalable PKI Management: Automated certificate lifecycle and revocation streamline fleet-wide secure firmware updates, reducing administrative overhead by 70%.
- Proven Threat Resilience: Comprehensive penetration testing and IEC 62443 compliance deliver robust protection against evolving IoT cyber threats, enhancing device longevity and compliance.
CONCLUSION
In summary, Embien's Secure FOTA solution revolutionized the Fortune 100 Industrial OEM's edge device ecosystem, fortifying i.MX6 gateways against cyber vulnerabilities while enabling seamless OTA and offline updates. By integrating secure boot, encrypted packages, PKI, and rollback features, we delivered a resilient, scalable framework that safeguards industrial IoT operations.
OEMs facing similar challenges in secure firmware updates, cyber secure edge devices, or IoT engineering, reach out to Embien today for tailored consultations and transform your threats into triumphs.