

The semiconductor industry is currently navigating one of its most significant architectural shifts in decades. The narrative around RISC-V has evolved from academic curiosity to a strategic imperative. The promise is clear: an open-source Instruction Set Architecture (ISA) that offers unprecedented "freedom", freedom from heavy licensing fees, freedom from restrictive vendor roadmaps, and freedom from the geopolitical risks of proprietary lock-ins like ARM or x86.
However, "free" in the context of an ISA does not mean "effortless." While the RISC-V revolution is well underway, the transition requires more than just picking an open core. For semiconductor design teams and embedded system developers, the real challenge lies in bridging the ecosystem gaps. Without a mature software stack, standardized verification processes, and robust development tools, teams risk facing integration hurdles that can balloon development costs and delay time-to-market.
In this article, we will explore the current state of the RISC-V ecosystem, identify the hurdles, and provide a prescriptive roadmap for a successful transition.
The global market for RISC-V technology is projected to reach over $26 billion by 2034, growing at a staggering CAGR of nearly 43%. This isn’t just hype; it’s a reflection of a fundamental shift in how chips are built.
Radical Cost Efficiency
In traditional proprietary models (ARM/x86), licensing and royalty fees can consume a significant portion of the Bill of Materials (BoM), especially for high-volume consumer electronics or IoT devices. RISC-V’s royalty-free model allows companies to redirect those funds toward customization and innovation.
Tailored Performance via Custom Extensions
Unlike the "one-size-fits-all" approach of proprietary ISAs, RISC-V is modular. You can implement the base integer set and add standard extensions (like 'M' for math or 'V' for vectors) or even create custom instruction set extensions. This is a game-changer for AI/ML edge inference, where domain-specific acceleration can provide a 10x lead in power efficiency.
Supply Chain Resilience and Sovereignty
In an era of export controls and trade tensions, RISC-V provides "Technology Sovereignty." Since the ISA is maintained by a neutral non-profit (RISC-V International based in Switzerland), it remains accessible regardless of geographical or political shifts.
While the ISA is finalized and robust, the surrounding ecosystem, the "connective tissue" of development, is still maturing.
The Verification Paradox
With great customization comes great verification responsibility. When you add custom instructions to a RISC-V core, you are essentially creating a new processor variant. Standard UVM (Universal Verification Methodology) testbenches are often insufficient. Teams must now navigate ISA compliance verification to ensure that their "optimized" core doesn't break standard software compatibility.
Software Stack Readiness
The "software gap" is often the most underestimated risk. While Linux support for RISC-V is now excellent, and RTOS options like FreeRTOS and Zephyr are maturing, the middleware layer, optimized libraries for DSP, AI, or security, can be fragmented. Porting legacy codebases from ARM to RISC-V requires a deep understanding of toolchain differences (GCC/LLVM) and hardware-software co-design.
To move from "experimentation" to "production-grade" RISC-V development, we recommend a phased readiness approach.
1. Architectural Assessment
2. Software & Toolchain Evaluation
3. Verification and Validation (V&V)
We are already seeing industry leaders making the leap.
At Embien, we have spent over 15 years helping global OEMs navigate complex architectural transitions. We recognize that moving to RISC-V is not just a hardware choice, it’s a software and systems integration challenge.
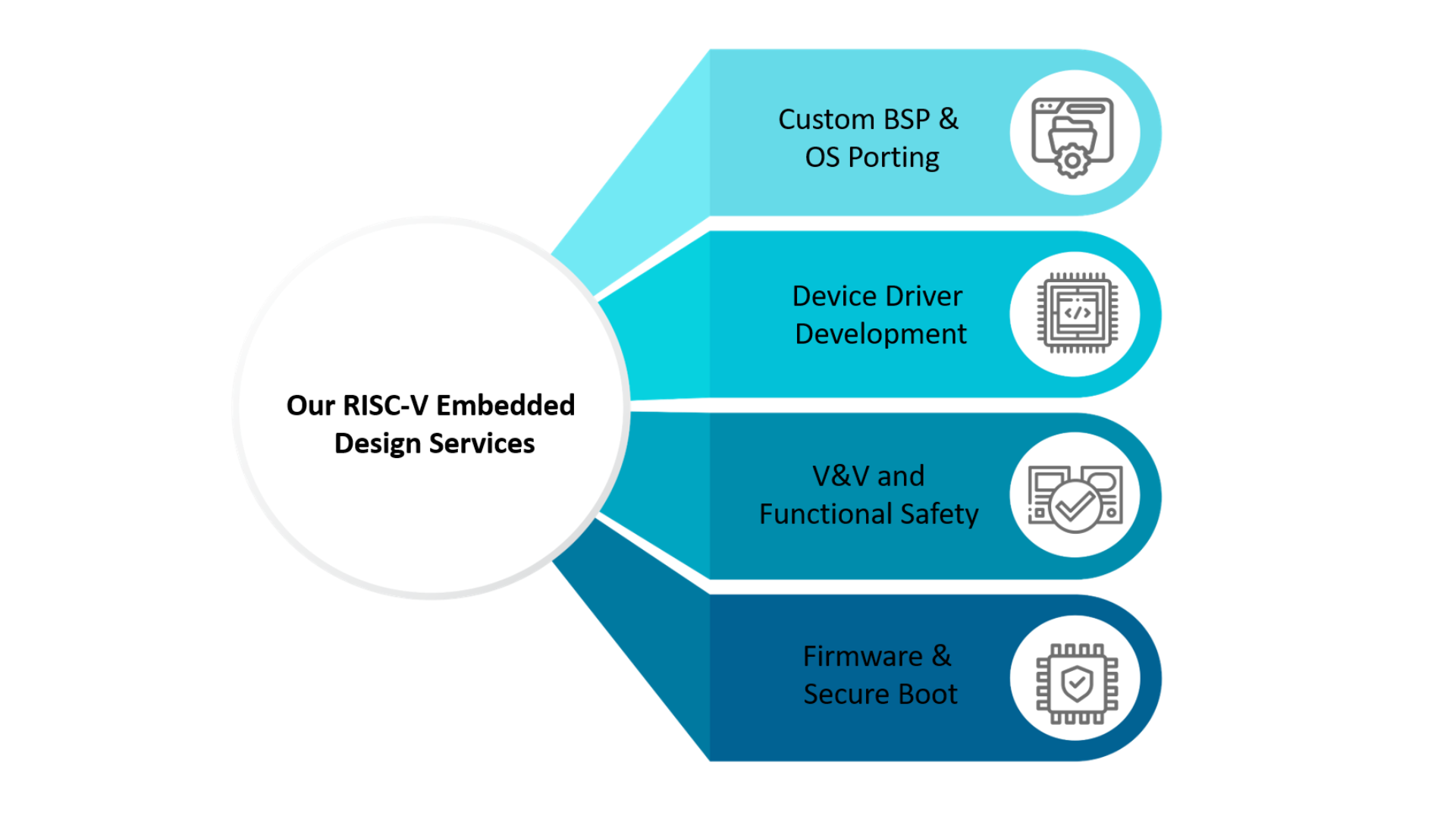
Our RISC-V Embedded Design Services are designed to eliminate the ecosystem hurdles mentioned above:
Challenges in Developing Embedded AI Systems
The future of embedded innovation is undoubtedly open. While the ecosystem gaps exist, they are being closed rapidly by a global community. With the right strategy and a partner who understands the nuances of the RISC-V software stack, your organization can turn "architectural freedom" into a tangible competitive advantage.

Electrical/electronic architecture, also known as EE architecture, is the intricate system that manages the flow of electrical and electronic signals within a vehicle.